The recent ransomware attack on Colonial Pipeline inspired a threat actor to create a new phishing lure to trick victims into downloading malicious files.
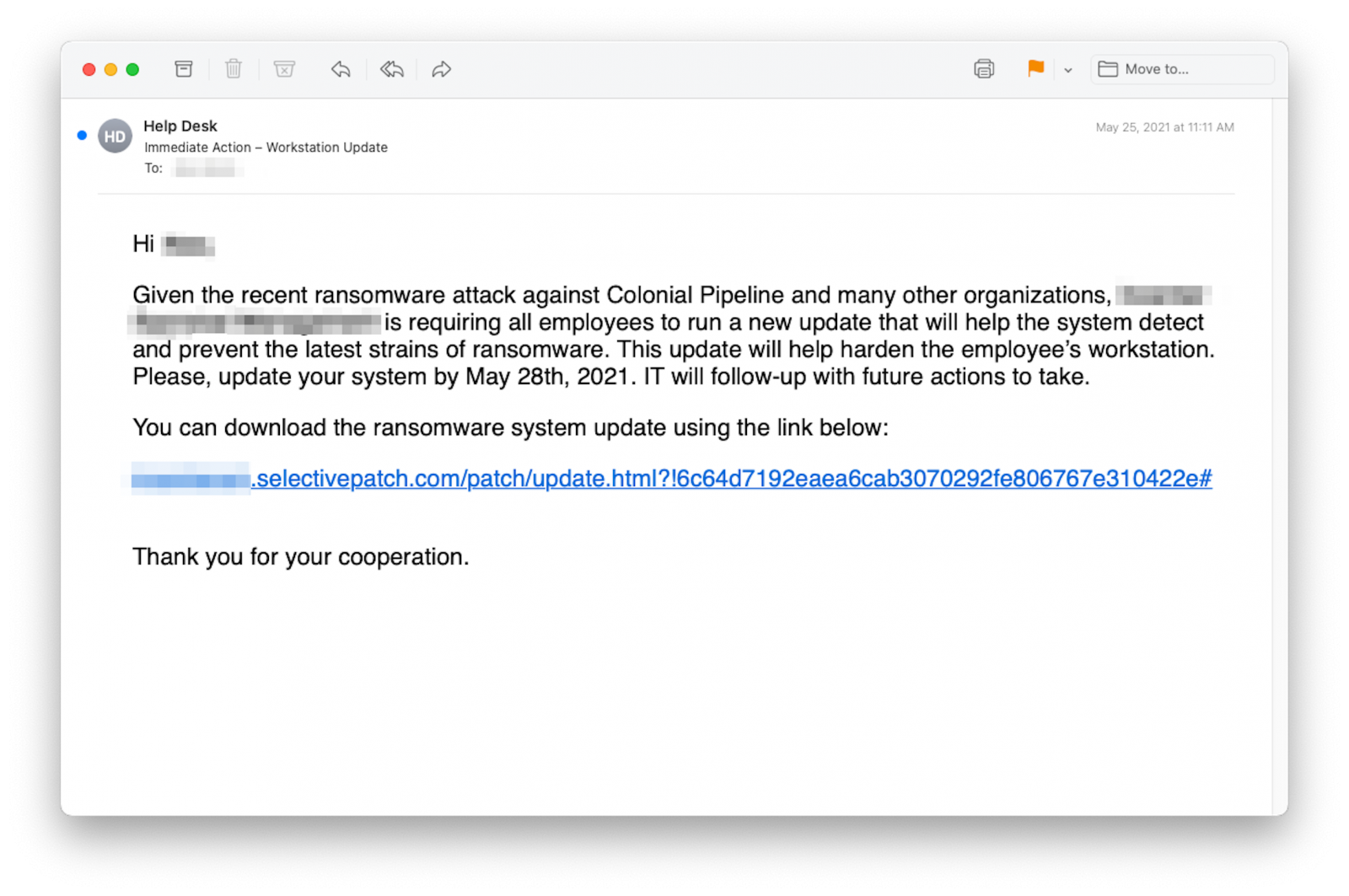
The emails are targeted and tailored as urgent notifications to download and install a system update that would defend against the latest ransomware strains.
Well-crafted emails
Threat actors did not lose much time after the Colonial Pipeline incident and used it as a theme in a new phishing campaign deployed a couple of weeks later.
Researchers at cloud-based email security platform INKY analyzed the attack which attempted to compromise computer systems using the Cobalt Strike penetration testing tool.
The fake emails use the Colonial Pipeline attack as an example of the devastating consequences a ransomware incident can have on an organization.
They urge recipients to install a system update from an external link to enable the system to “detect and prevent the latest strains of ransomware.” A deadline for applying the update is also provided, to increase urgency.
Cobalt Strike inside
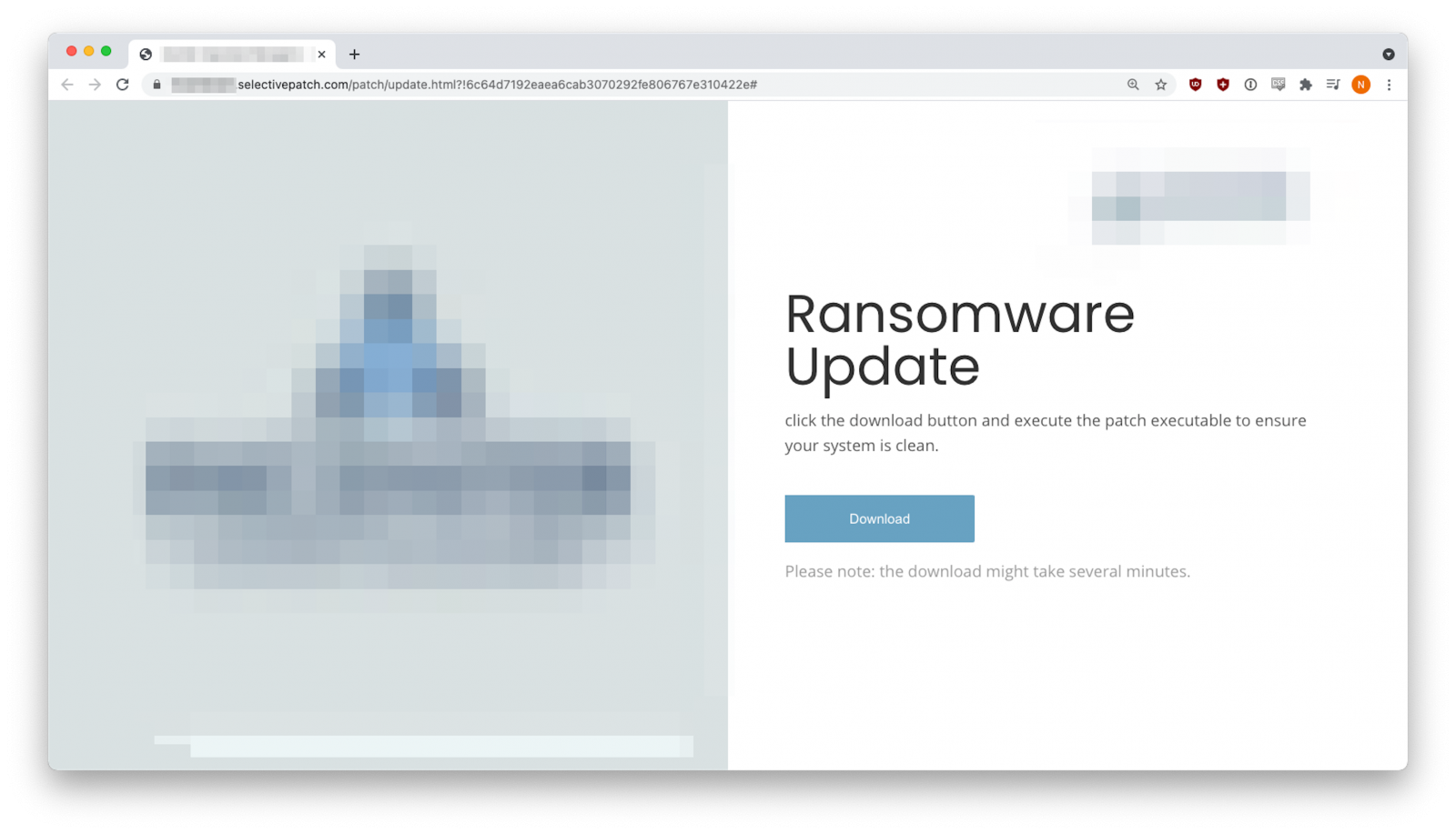
The threat actor used domains that are easy to mistake for legitimate ones (ms-sysupdate[.]com and selectivepatch[.]com), registered towards the end of May through Namecheap.
INKY researchers note that the two domains were used for sending the malicious emails as well as for hosting the fake “ransomware update” executables.
Furthermore, in both cases the download pages were customized with the target company’s logo and imagery, to make them appear trustworthy.
INKY researchers say in a blog post today that the payload was Cobalt Strike, a threat emulation software developed for penetration testing purposes but often used by malicious actors, too, especially in the ransomware business.
Read full article: https://www.bleepingcomputer.com/news/security/phishing-uses-colonial-pipeline-ransomware-lures-to-infect-victims/


