I’ve been working in email security for several years now, and every once in a while I will still get an email that is so authentic looking, even I get fooled. The timing of this email couldn’t be more impeccable, because I am actually expecting an email internally that would look just like this. Fortunately, we use our own technology and have INKY in place. She was smart enough to inspect this email in seconds, determine that it was dangerous, and throw a red banner flag up to make me pause before taking action on the email.
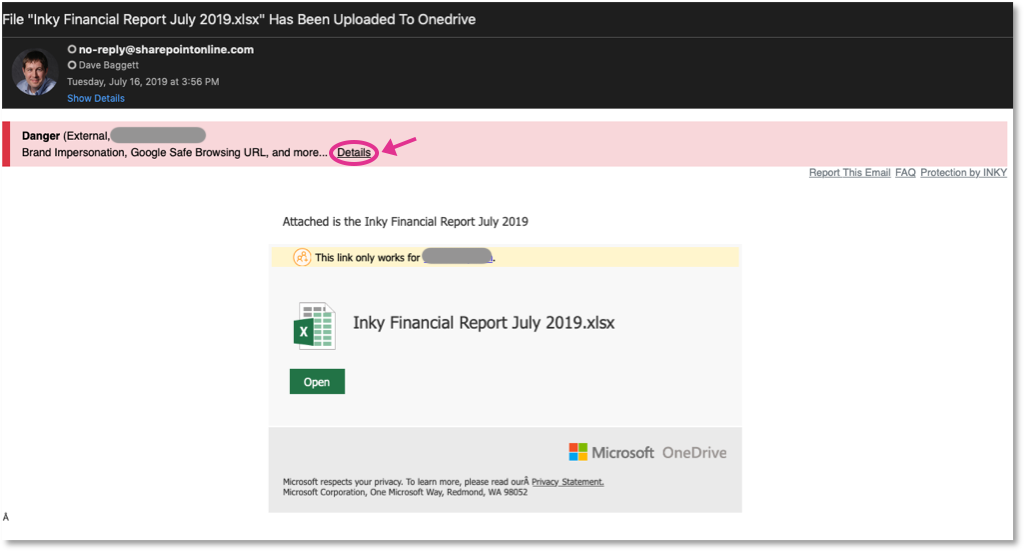
When I clicked the "Details" link in the red banner, it listed the many reasons this email was flagged:
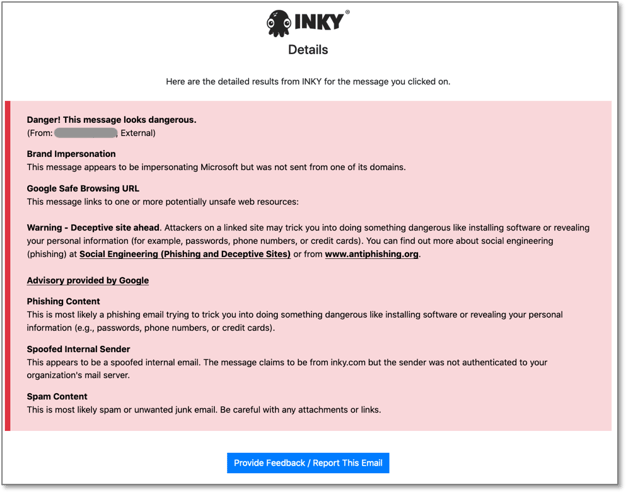
Notice how this has been reported to Google Safe Browsing and other threat feeds? Great. But what happens when your user receives this zero day, before anyone else has reported it? INKY still would have caught this brand impersonation.
And what would have happened if I had clicked the green "Open" button in this phishing email? INKY would have protected me by displaying a screenshot of where the link actually goes. In this case, it led to a convincing-looking Microsoft Office 365 login form. However, it is easy to see another red banner and another warning that visiting this site may not be safe:
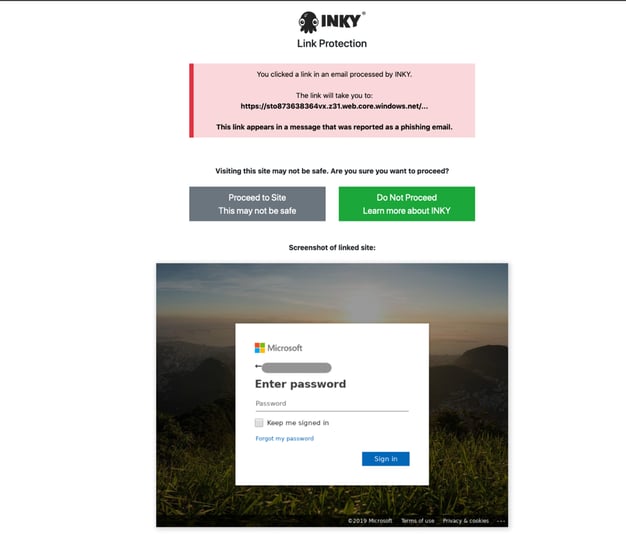
INKY's banner system prevents humans from making mistakes, because the only way to proceed to this dangerous site is to click a button acknowledging that "This may not be safe." Customers can also opt to quarantine the emails that INKY classifies as dangerous so that they are not delivered.
I am well-trained on email security, yet even I almost clicked on the attachment in this email. I'm grateful we build technology that is solving the phishing problem better than anything else out there. See for yourself, schedule a demo.



