Just when we think we've seen it all, we block a clever but dangerous phishing technique like this one. We call this "Phishception" because, like the layered storyline of the movie "Inception", here the phish is found nested within another phishing email.
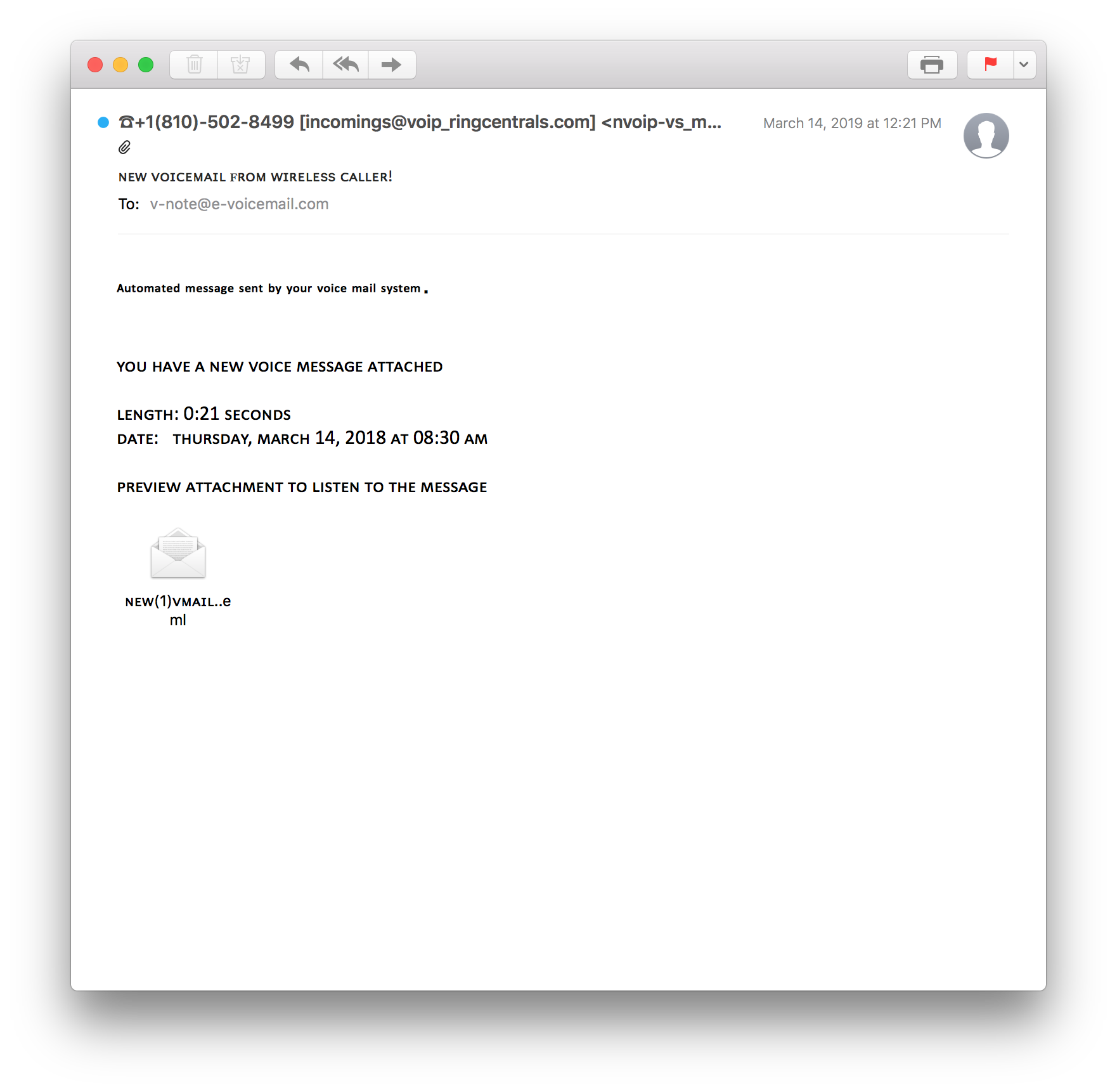
The first email looks like a benign notice of new voicemail message. It has no brand indications to analyze or links to scan, just a mail file to click to purportedly listen to a voicemail message:
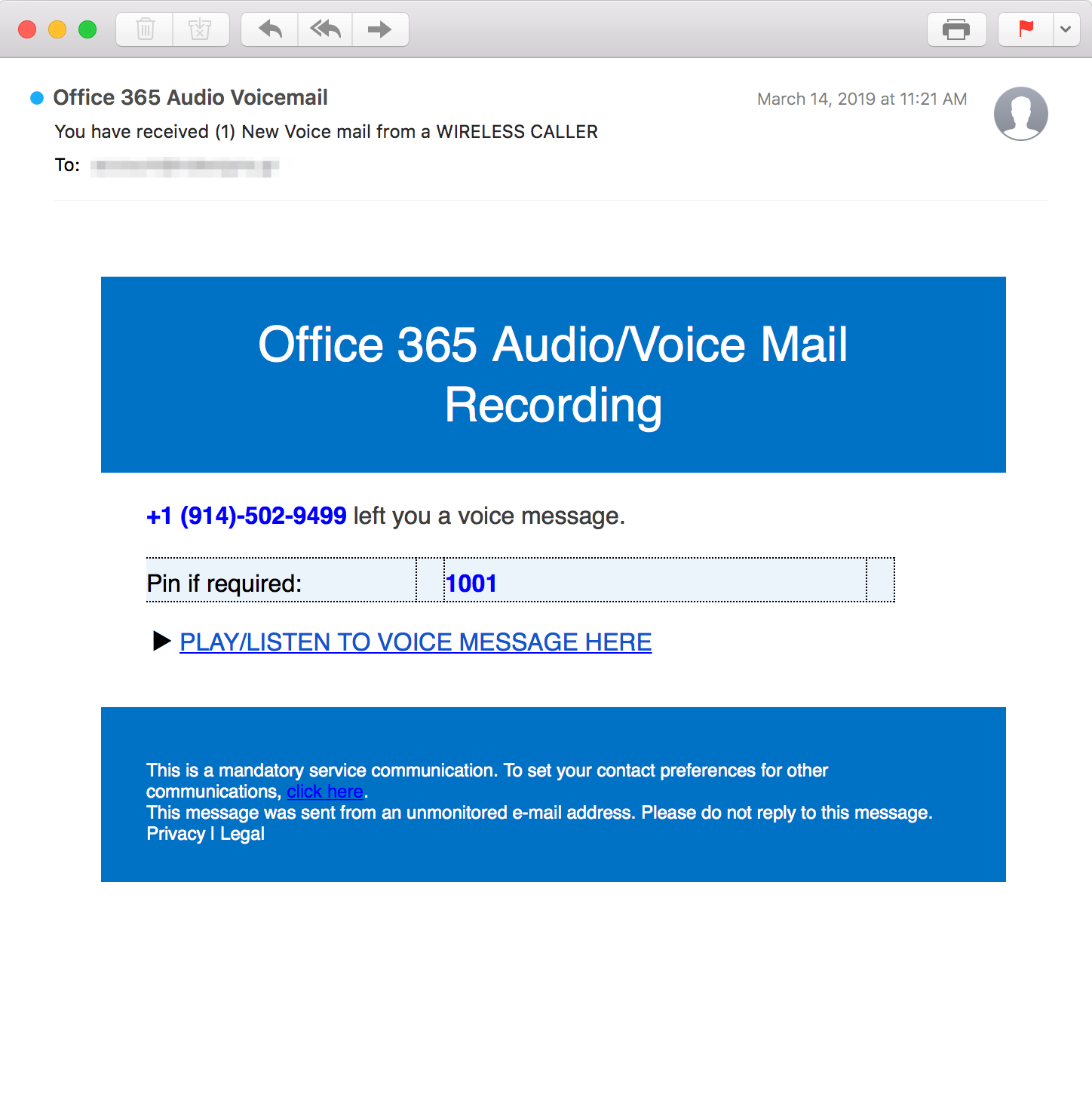
Clicking that .eml file doesn't immediately launch any malware like many phishing emails with attachments. Instead, it takes the recipient to what seems to be an an email from Office 365 Audio Voicemail. The body of the email has a harmless-looking "PLAY/LISTEN TO VOICEMAIL HERE" link and a phone number:
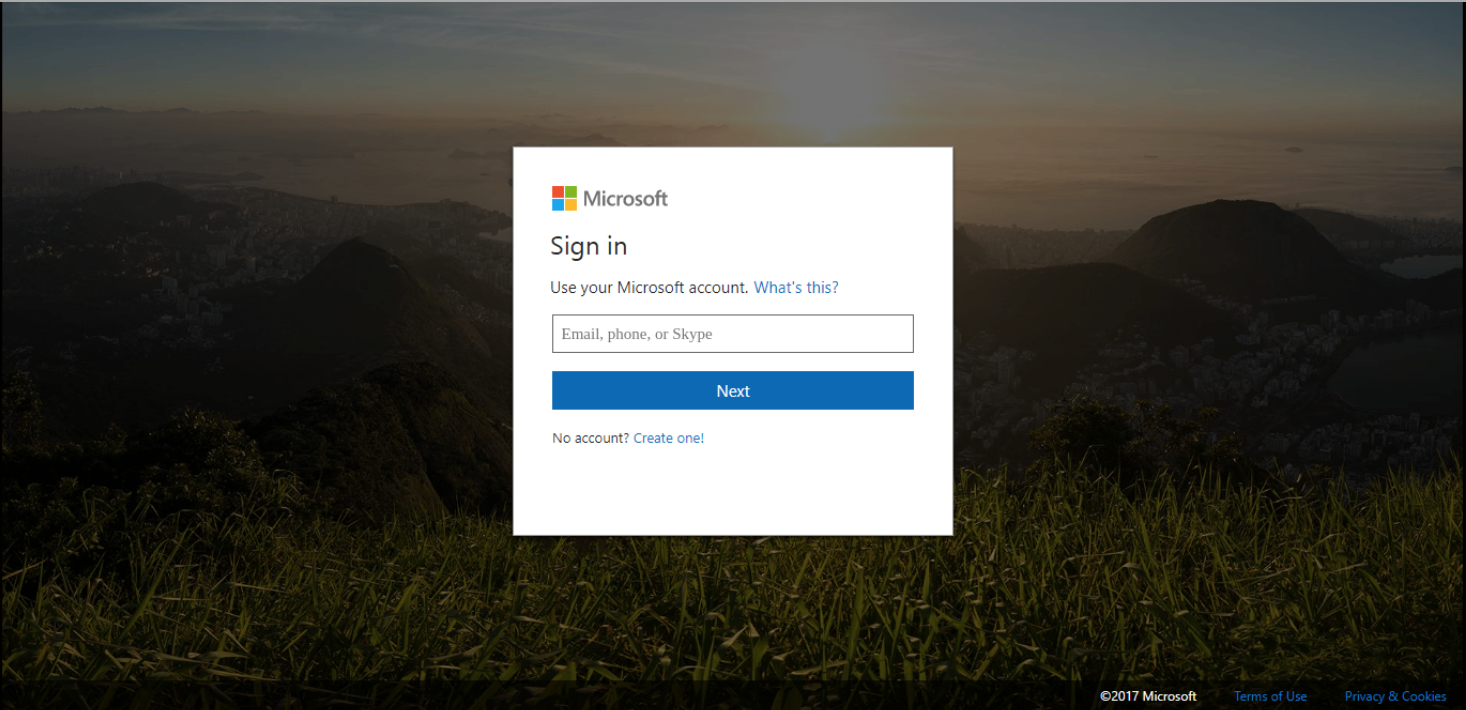
The danger lies in clicking the blue voicemail link. If the recipient clicked it, they would be redirected to a fake Microsoft login page created by criminals to steal email credentials. After the login form is used, the attacker stores this information in their database and the recipient is redirected to a real Microsoft page to avoid detection. Here is the official-looking fake Microsoft Office 365 login page:
Fortunately, this person is an INKY customer. Because INKY goes deeper than other mail protections, by looking inside HTML attachments, our customer was safe. INKY displayed this prominent red "Danger" banner at the top of the initial email:
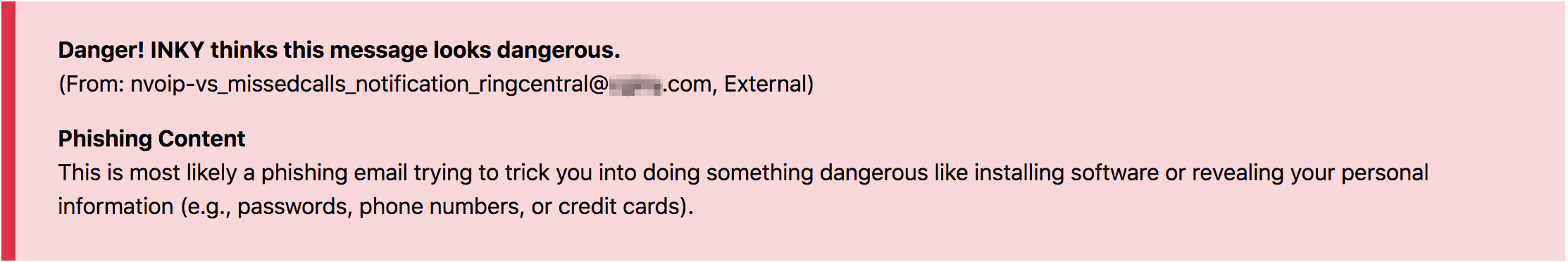
These color-coded banners tell the user exactly why a particular email is suspicious or dangerous, so users are protected and educated. This red Danger banner says, "This is most likely a phishing email trying to trick you into doing something dangerous..." Customers also have the option of quarantining the dangerous emails.
INKY users don’t have to stay on top of phishing trends, because we do it for them. For more email security tips and breaking news, follow INKY on LinkedIn.


