Scammers are sending phishing, spear phishing, and whaling emails in record numbers. A recent Internet Threat Security Report shows that 1 out of every 131 emails contained some form of malware. The hackers are nothing if not proficient. 76% of businesses report being a victim of phishing attacks and the business costs are staggering.
What is Phishing?
The name “Phishing” comes from the early days of America Online (AOL). Scammers sent out email “lures” trying to hook unsuspecting users and snare their passwords or financial data. Hackers send out legitimate-looking emails that contain a link to a spoof website, or an attachment with malware or malicious code included.
While originally targeted at individual users, attacks have gotten more sophisticated and now are commonly target at companies to gain network access, launch malware and ransomware attacks, and aim directly at C-level executives.
Examples of Phishing
The most common phishing attack is a fake invoice, requesting payment, in an attempt to get a click. Other phishing attempts include fake purchase orders, scanned documents that appear to come from office printers, email delivery notices, shipping delivery notices, and notices from company IT departments.
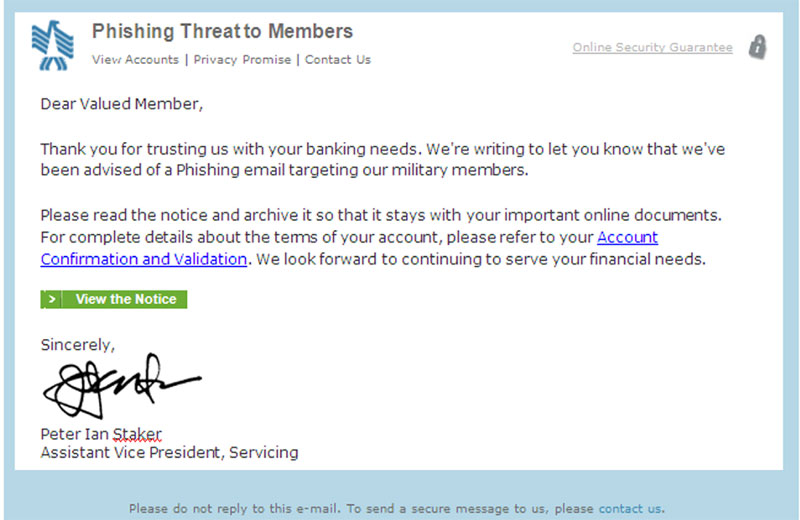
Here is a sneaky phishing attack, which targets military members. It appears to come from their financial institution and warns them of phishing attempts with a link to confirm account information, which is, of course, fake.
What is Spear Phishing?
While phishing schemes are typically mass mailings, spear phishing is a more targeted and customized attack. The bad guys will do a little research and find out specific information about the target. It may be from the company website, social media, financial reports, or industry sources. With the information in hand, they will customize an email to make it appear more legitimate.
Examples of Spear Phishing
It may address recipients by name, reference others in the company, or mention a current project or proposal – anything to get people to click on an attachment to launch the attack.
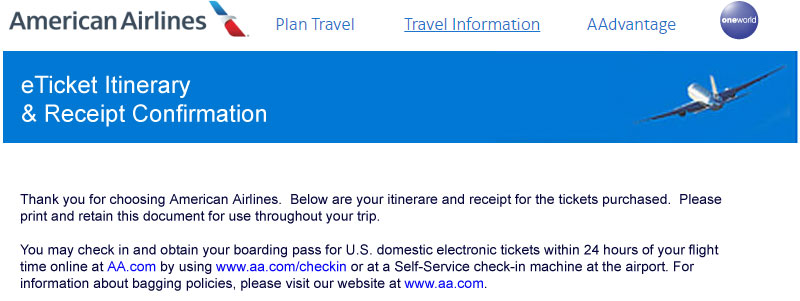
A particularly nasty spear phishing attack is disguised as airline flight confirmations often with specific flight information from booked trips. These emails come from a spoofed email such as a travel agent, airline, or HR department, and has an astonishing 90% reported success rate.
What is Whaling?
Whaling is a form of spear phishing aimed at “whales” at the top of the food chain. Whaling targets CEO’s, CFO’s, and other high-level executives. This type of cyber attack is big business for the hackers. The FBI counts more than $5 billion in losses, and more than 24,000 victims have been tricked by this scam over a three-year period.
Examples of Whaling
There are a variety of tax scams, including impersonating company execs and asking for W-2 forms or employee financial data to file fake tax returns and grab refunds. In other scenarios, an email appearing to come from the company CEO or COO directs the accounting department to complete wire transfers. They come from legitimate-sounding email addresses or spoofed emails and mix in the right names and details to make it sound legitimate.
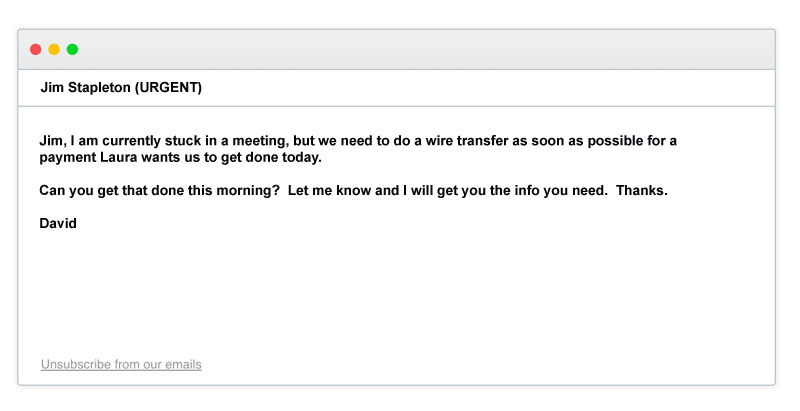
These are specific, targeted, and sophisticated attacks that can fool even the biggest tech companies, including Google and Facebook who were hit by a reported $100 million.
What Do These Cyber Attacks Mean for My Business
If this cyber attacks are not dealt with, it means trouble for the business. The most likely impacts are financial and corporate reputation.
Scammers are sending record numbers of these phishing emails. 30% get opened. 12% click on a malicious link or attachment. That means no matter how much education you do with your employees, some of them are going to ignore what you tell them. Nearly all the companies that fell victim suffered financial damage. Experts estimate the total damage done to U.S. businesses approaches half a billion dollars a year.
The prime targets weren’t just unsuspecting employees. The overwhelming number of attacks were aimed at IT departments and finance departments.
There Is A Phishing Solution
Anti-Phishing Solution by Inky provides the most comprehensive malware and email phishing protection available.
- Inky® Phish Fence uses a sophisticated mix of algorithms, Machine Learning and Computer Vision that block even deep-sea phishing attacks that may get past other systems.
- Inky® Phish Fence scans every internal and external email automatically to flag malicious emails.
- Unlike any other anti-phishing system on the market today, Inky® Phish Fence uses proprietary technology and algorithms to “see” each email much as the end user would. Unlike a person, it can tell when an email is a forgery, and can send it to quarantine, or deliver it with disabled links and warnings.
- Reporting of phishing emails show within the email itself, which allows the phishing attack to be viewed on either on the desktop or a mobile device.
- A comprehensive dashboard allows admins to see an overview and to drill down to individual messages to target specific attacks. Admins can search by date, date rangers, users, or specific types of attacks.
- Inky® Phish Fence will sit on top of any email system, including Microsoft Office 365, Exchange, and Google Suite. It can be set up in just a couple of hours.
To see Inky’s anti-phishing solution in action, request a demo and let us show you what a difference it can make.
This blog was updated on October 5, 2021, and can be found here.



